Eliminate Risk of Failure with Cisco 300-215 Exam Dumps
Schedule your time wisely to provide yourself sufficient time each day to prepare for the Cisco 300-215 exam. Make time each day to study in a quiet place, as you'll need to thoroughly cover the material for the Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies exam. Our actual Cisco Certified CyberOps Professional exam dumps help you in your preparation. Prepare for the Cisco 300-215 exam with our 300-215 dumps every day if you want to succeed on your first try.
All Study Materials
Instant Downloads
24/7 costomer support
Satisfaction Guaranteed
An organization recovered from a recent ransomware outbreak that resulted in significant business damage. Leadership requested a report that identifies the problems that triggered the incident and the security team's approach to address these problems to prevent a reoccurrence. Which components of the incident should an engineer analyze first for this report?
Refer to the exhibit.
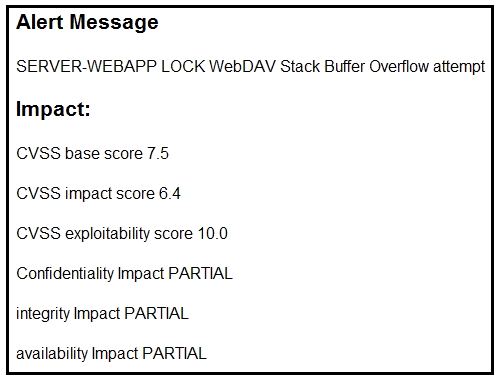
After a cyber attack, an engineer is analyzing an alert that was missed on the intrusion detection system. The attack exploited a vulnerability in a business critical, web-based application and violated its availability. Which two migration techniques should the engineer recommend? (Choose two.)
Refer to the exhibit.
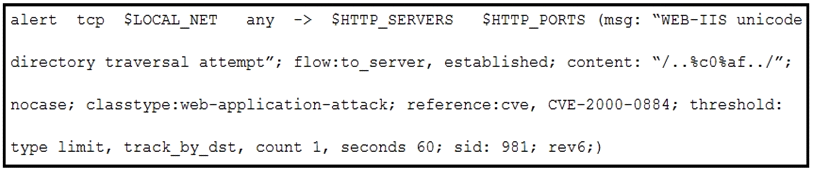
A company that uses only the Unix platform implemented an intrusion detection system. After the initial configuration, the number of alerts is overwhelming, and an engineer needs to analyze and classify the alerts. The highest number of alerts were generated from the signature shown in the exhibit. Which classification should the engineer assign to this event?
Refer to the exhibit.
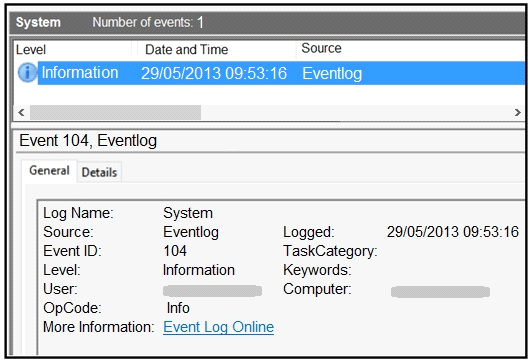
An employee notices unexpected changes and setting modifications on their workstation and creates an incident ticket. A support specialist checks processes and services but does not identify anything suspicious. The ticket was escalated to an analyst who reviewed this event log and also discovered that the workstation had multiple large data dumps on network shares. What should be determined from this information?
An engineer is analyzing a ticket for an unexpected server shutdown and discovers that the web-server ran out of useable memory and crashed.
Which data is needed for further investigation?
Are You Looking for More Updated and Actual Cisco 300-215 Exam Questions?
If you want a more premium set of actual Cisco 300-215 Exam Questions then you can get them at the most affordable price. Premium Cisco Certified CyberOps Professional exam questions are based on the official syllabus of the Cisco 300-215 exam. They also have a high probability of coming up in the actual Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies exam.
You will also get free updates for 90 days with our premium Cisco 300-215 exam. If there is a change in the syllabus of Cisco 300-215 exam our subject matter experts always update it accordingly.
